WireGuard is an open-source, fast VPN, that uses state-of-the-art cryptography. Vpn stands for Virtual Private Network. If you compare Wireguard VPN to other VPN solutions, WireGuard VPN is easily configured, smaller footprint, and is faster. Other VPN solutions are IPsec and OpenVPN. WireGuard can be installed on any major operating system like Windows, Linux, macOS, and Android.
When we go into the depth of WireGuard VPN, we find that it does not follow the client-server model but follows peer-to-peer VPN. we can set a peer to be a client or a server during configuration. It creates a network interface on each peer device. This then works as a tunnel. Peer authentication is done by sharing or validating public keys. It mimics the SSh model.
Let’s jump to the main topic of this article which is to set up wireguard VPN on Debian 11. It will act as a VPN server.
Step1: Installing WireGuard on Debian 11
Let’s start by installing the wireguard VPN first. It can be installed via backports repositories. We can add it to our system by the following command:
$ echo 'deb http://ftp.debian.org/debian buster-backports main' | sudo tee /etc/apt/sources.list.d/buster-backports.list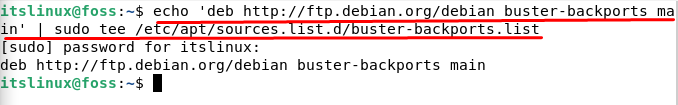
Now that the repository has been enabled, let’s update our apt-cache. For this purpose type the following command:
$ sudo apt update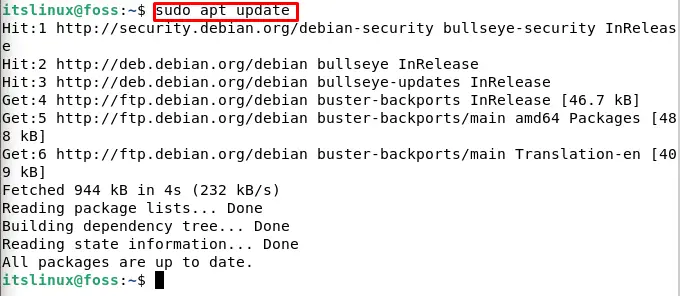
After updating we have to install the wireguard module and tools. For this purpose type or copy the following command:
$ sudo apt install wireguard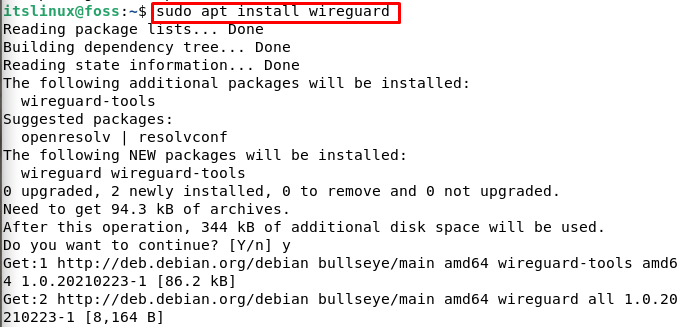
It should be noted that wireguard runs as a kernel module.
Step2: WireGuard Configuration
Now that we have installed wireguard in Debian 11, let’s configure wireguard. The wg and the wg-quick commands help us in managing and configuring wireguard.
As we mentioned in the introduction part of this article, every device in the Wireguard VPN network has a public and private key. For this purpose we have to run the following command to generate key pair:
$ wg genkey | sudo tee /etc/wireguard/privatekey | wg pubkey | sudo tee /etc/wireguard/publickey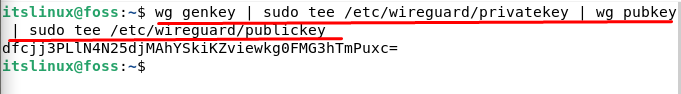
You will be able to see the key once you run the above command just like shown in the screenshot. The key pair files were generated in the /etc/wireguard directory. We can view file content using the cat or less commands in Debian 11.
It should be noted that the private key is private and should never be shared with anyone.
Another key which wireguard supports is the pre-shared key. The function of this key is to add an extra layer of symmetric key cryptography. It should be kept in mind that this key is completely optional. Also, this key should be unique for every peer pair.
The next step in configuring WireGuard is to configure the tunnel device. The tunnel device will be able to route our VPN traffic. For this purpose let’s set up our device from the command line interface.
We will open the editor and create a new file with the name wg0.conf. To create the configuration we have to use a text editor. Follow the following command to open the editor and create a new file:
$ sudo nano /etc/wireguard/wg0.conf
Add the following in your open editor:
Address = 10.0.0.1/24
SaveConfig = true
ListenPort = 51820
PrivateKey = SERVER_PRIVATE_KEY
PostUp = iptables -A FORWARD -i %i -j ACCEPT; iptables -t nat -A POSTROUTING -o enp0s3 -j MASQUERADE
PostDown = iptables -D FORWARD -i %i -j ACCEPT; iptables -t nat -D POSTROUTING -o enp0s3 -j MASQUERADE
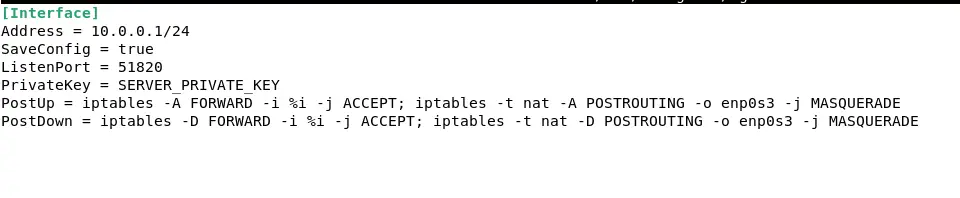
Press CTRL+S to save the file and after that press, CTRL+X to close the file.
Before going forward let me stress on the point that you have to replace the SERVER_PRIVATE_KEY in the above code with your private key. You can generate a private key with the following command:
$ umask 077 /etc/wireguard
$ wg genkey | tee privatekey | wg pubkey > publickeyTo view the private key you can follow the following command:
$ sudo cat /etc/wireguard/privatekeyKeep in mind that in the above commands you have to replace enp0s3 which is located after the Postrouting with the public network interface. You can find your public interface with the following command:
$ ip -o -4 route show to default | awk '{print $5}'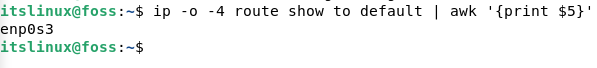
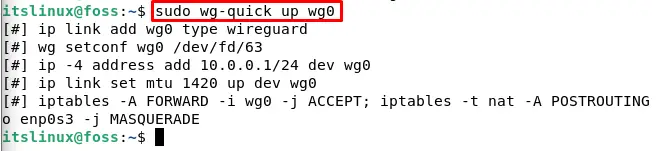
Now that you are done with editing the file in the editor, using the attributes in the config file we have to bring the wg0 interface up. For this purpose type the following command:
$ sudo wg-quick up wg0The output will be like shown below:
We can view the configuration and the interface state with the following command:
$ sudo wg show wg0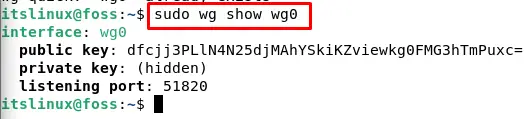
The last step in configuring wireGuard is to bring it at boot time. The reason behind this is that WireGuard is manageable with systemd. Type the following command:
$ sudo systemctl enable wg-quick@wg0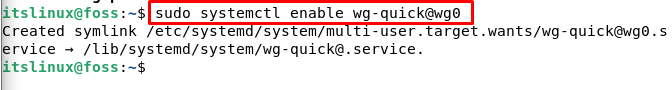
Step3: Server Networking and Configuration of Firewall
This step involves configuring firewall and server networking. To make NAT work you have to first enable the IP forwarding. For this purpose type the following command:
$ sudo nano /etc/sysctl.confThis will open the sysctl.conf file. We have to add the following line in that file:
net.ipv4.ip_forward=1When you are done adding the above line, save the file by pressing CTRL+S and then to close the file press CTRL+X.
After this type the following command in the terminal:
$ sudo sysctl -p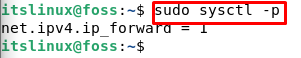
The final step is to manage our firewall. We have to open port 51820 for UDP traffic. This is only if one is using the UFW. For this purpose type the following command:
$ sudo ufw allow 51820/udp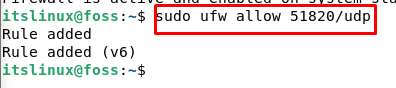
Congratulations! We have successfully set up the Debian peer. It will now act as a server.
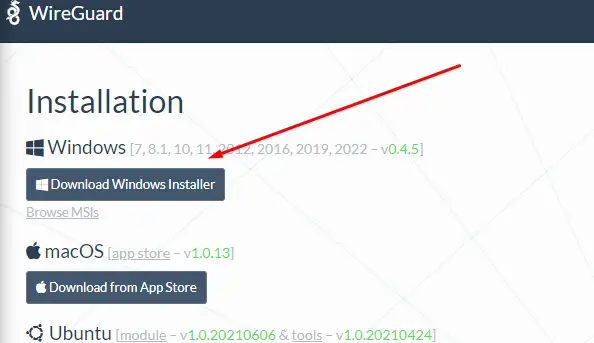
Step4: Setup of Windows Client
Now as the server is set up, we have to set up a client. For this purpose we choose windows. Go to your browser and install the MSI package for the window from the following link:
https://www.wireguard.com/install/
Install the downloaded file and after that click in the “Add Tunnel” in the bottom left corner.
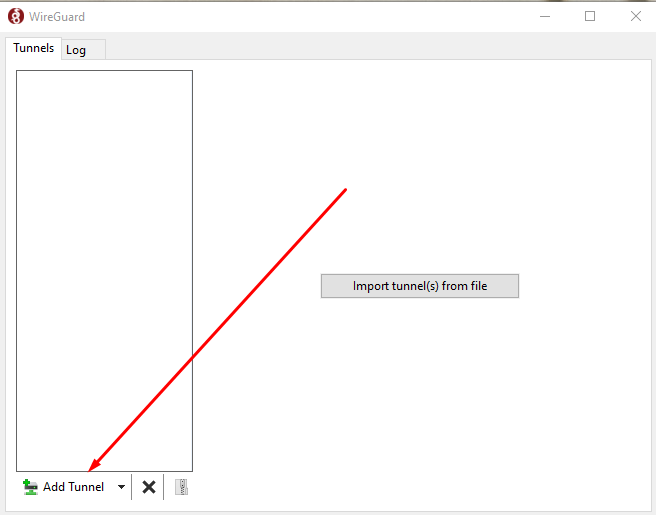
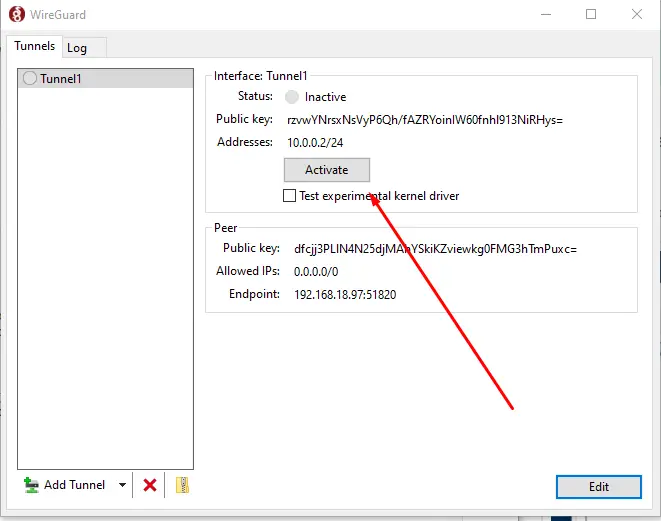
A dropdown window will open. Select the option of “Add empty tunnel”. Once done you will see the following screen:
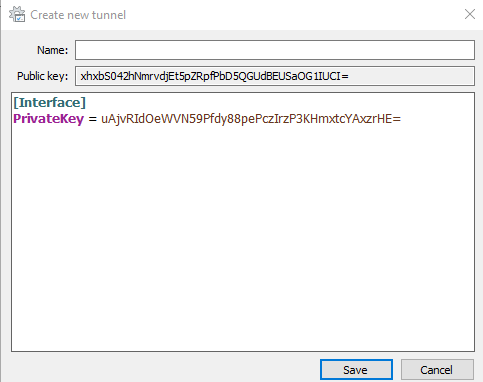
Here edit the file by adding the following lines:
[Interface]
PrivateKey = CLIENT_PRIVATE_KEY
Address = 10.0.0.2/24
[Peer]
PublicKey = SERVER_PUBLIC_KEY
Endpoint = SERVER_IP_ADDRESS:51820
AllowedIPs = 0.0.0.0/0
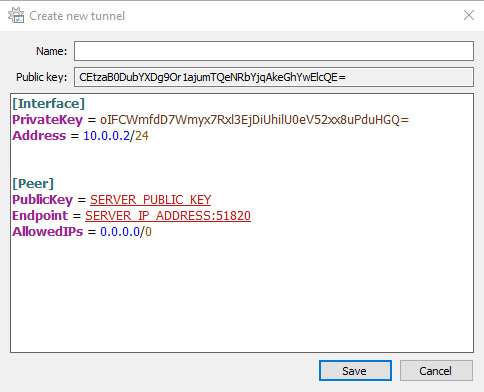
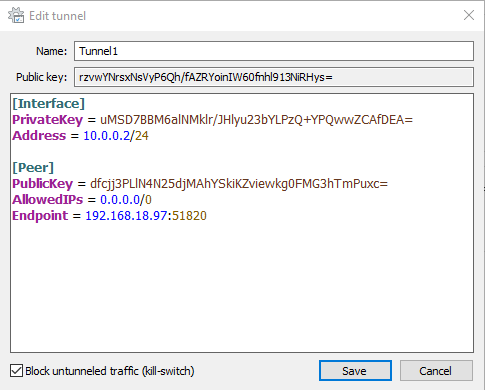
You should keep in mind that you have to add your private key as well as the server you created, it’s a public key in the respective fields. Also, you have to replace the “Server_IP_ADDRESS” keyword and place the server IP address. After this, set the name and click on save.
Step5: Client Peer and Server Connection
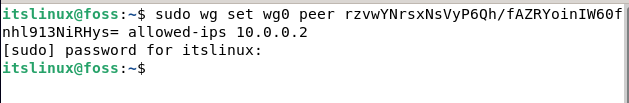
Step5 is to add the client and the server. This is the second last step where we will set the IP address and the public key of the client to the server. Go back to your Debian 11 server and type the following command:
$ sudo wg set wg0 peer CLIENT_PUBLIC_KEY allowed-ips 10.0.0.2Replace the public key with your client’s public key. You can find the client public key on your window WireGuard Application.
If you have done all the previous steps, then go to your client machine i-e windows WireGuard App.
Step6: Windows Client
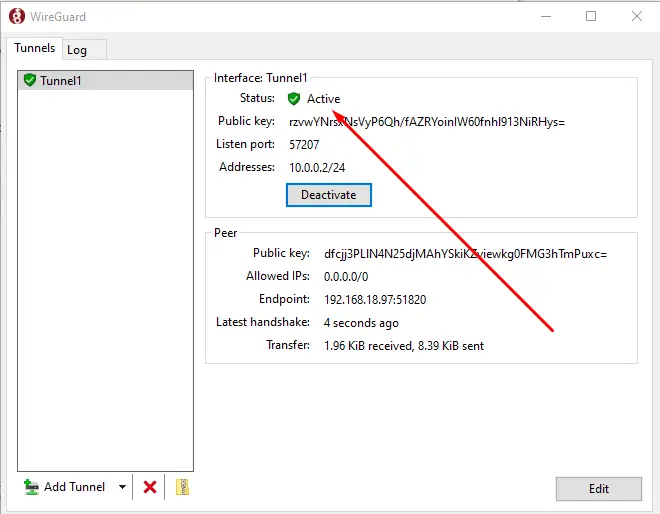
This is the last step where you just have to click on the button that says “Activate” in the WireGuard App tunnel.
Once you click on the activate button, the tunnel status will automatically change to Active. And with this, we are done. Congratulations!
Conclusion
We have installed and configured WireGuard on Debian 11. We made the Debian machine as a server and the windows machine acted as a client.
Now you can easily create a tunnel that is secured as well as encrypted handling all the internet traffic. In simple words, you will be able to browse and surf the internet anonymously. This will help in shielding you from everyone including hackers as the data traffic is private.

TUTORIALS ON LINUX, PROGRAMMING & TECHNOLOGY