In Linux, tcpdump is a user-friendly open-source tool that acts as a network packet analyzer for troubleshooting and identifying network problems. It is very helpful for diagnosing and debugging connectivity issues over the internet connection.
Let’s discuss the efficient use of the tcpdump command using different examples.
How to Use TCPDUMP in Linux?
As discussed earlier, the tcpdump is a command line tool; its working/usage depends on the syntax written below:
$ tcpdump [Options]
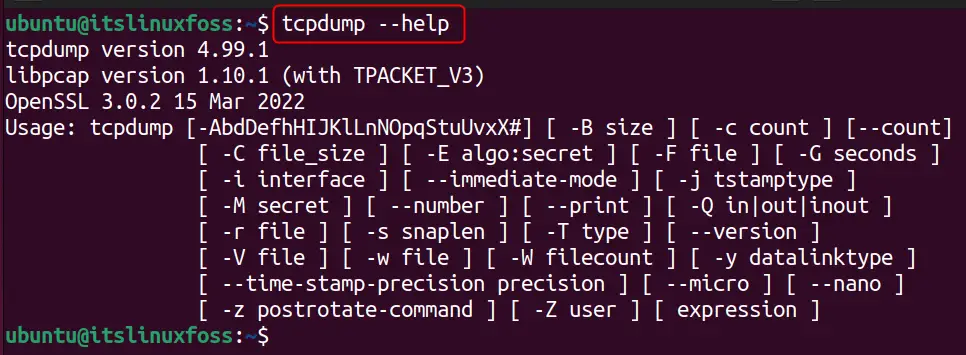
The options supported by the tcpdump command can be obtained using the command provided below:
$ tcpdump --help
Now, let’s have a look at the usage of the tcpdump through examples.
Example 1: Capture Real-time Network Data Packets
The tcpdump command can capture and display the network packets in real time. It shows different details about the data packets, such as interface type, IP address, captured data size for every packet, etc., as shown below:
$ sudo tcpdump
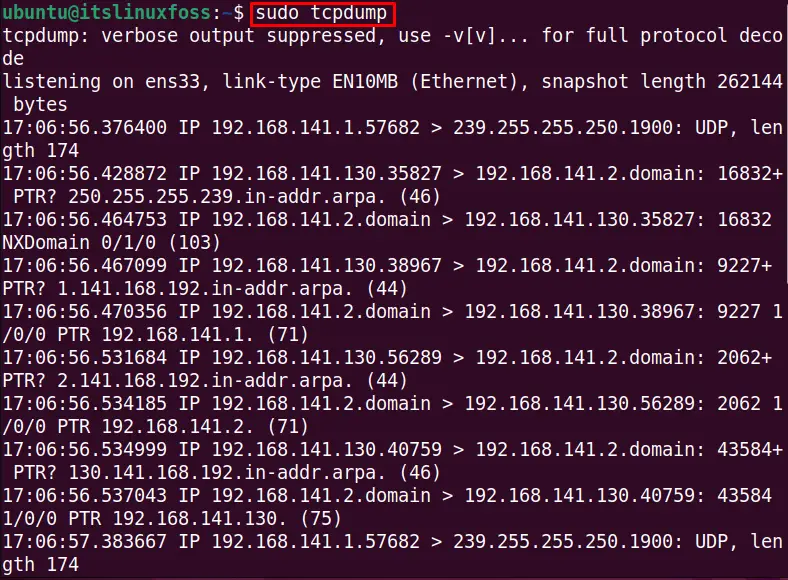
The data packets are captured in real-time, and their information is shown in the output.
Example 2: Check the Supported Interfaces Using tcpdump
There are several interfaces utilized to capture the data packets over the internet. To get a list of interfaces, use the “D” option with the tcpdump command, as done with the following command:
Note: This command requires the “root” permissions to access the data.
$ sudo tcpdump -D
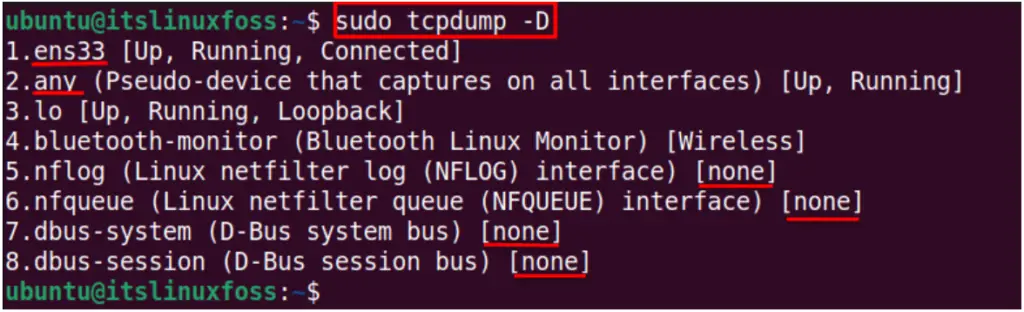
The output shows that the system has 8 interfaces and is connected to “ens33”. The “any” interface is also running for other system services. The “none” status shows that these interfaces are currently inactive.
Example 3: Capture Data Packets for Specific Interface
The “i” option is used to specify the interface in which you want to display the data as shown in the below command:
$ sudo tcpdump -i ens33
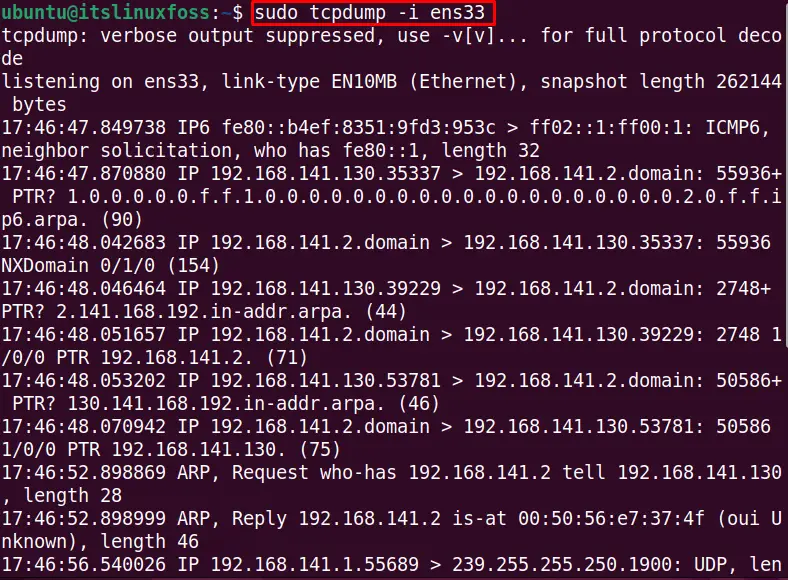
The output shows the details about the ens33 interface only.
Example 4: Capture Limited Data Packets Using tcpdump
Data packets are collected to a specific limit by the “c” (count) option of the tcpdump command. Using the following command, you can fetch the three (3) data packets only:
$ sudo tcpdump -i any -c3
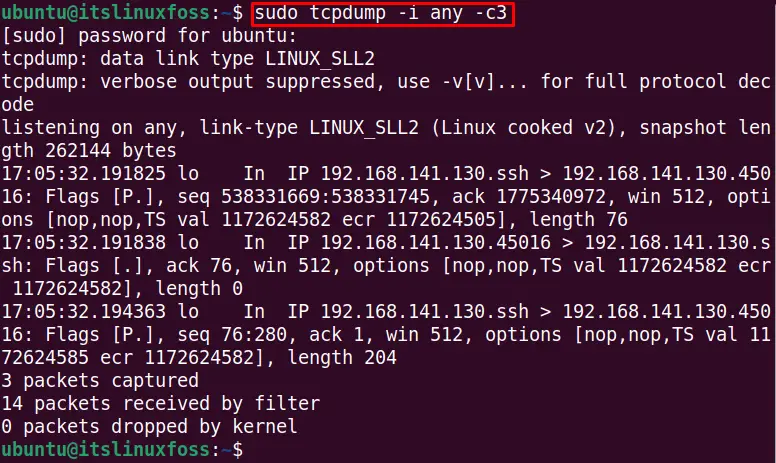
It captures the information for three data packets, as seen in the output.
Example 5: Store the Data Packets Information to a Specific File
If you want to store the real-time data pockets information in raw form into a file, use the “w” option with the specified filename. For instance, the below command captures the data for the ens33 interface into the file “testfile.txt”:
$ sudo tcpdump -i -ens33 -w testfile.txt
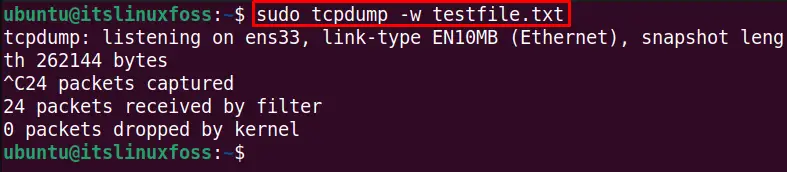
The information is stored in the testfile.txt file, which can be displayed with the below cat command:
$ cat testfile.txt
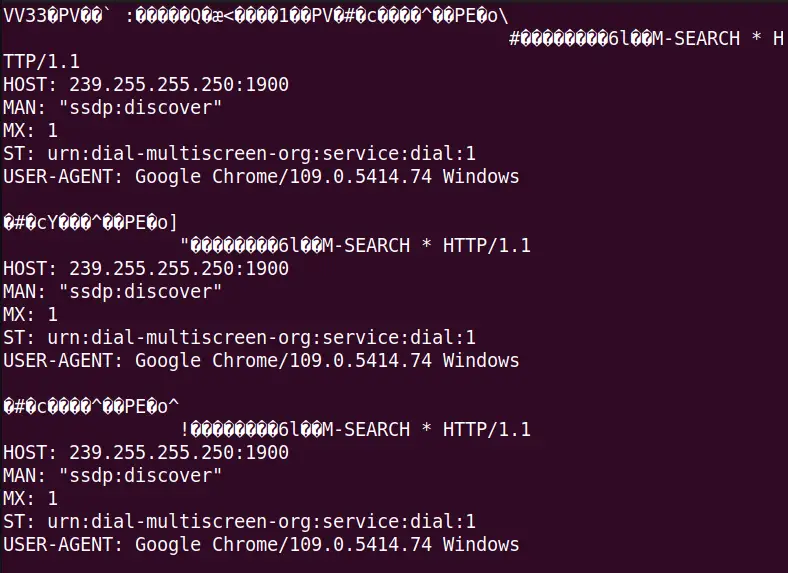
The output shows the data packet information in binary format.
Example 6: Read the Data Packets Information From a File
The previous example stores the information in binary format (raw data) into testfile.txt. The binary data can be converted into the human-readable format by using the “r” option with the specified filename:
$ sudo tcpdump -r testfile.txt
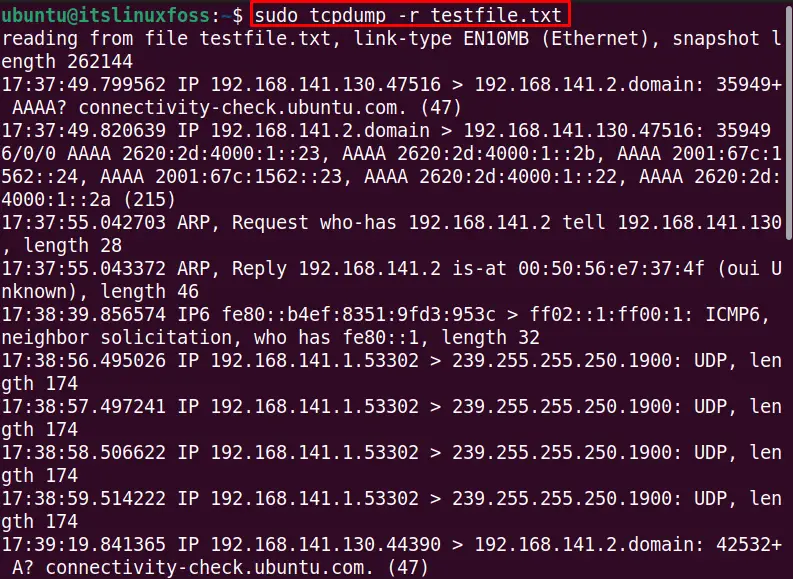
The output displays the data in a human-readable format.
Example 7: Capture Packet From Specific Port
The specific port number can be used to capture the data, which tells us the information about the domain name server. To check the system’s DNS level communication with the ens33 interface, use port number 80 with the below tcpdump command:
$ sudo tcpdump -i ens33 port 80
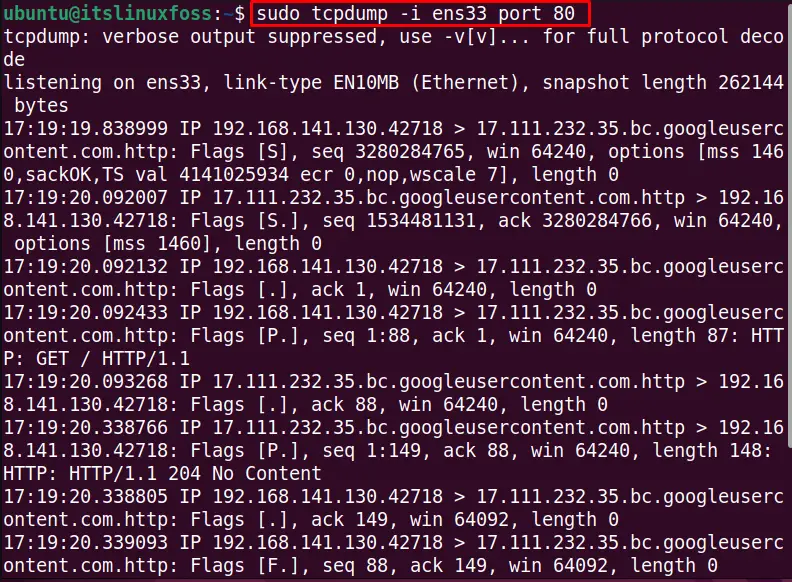
It displays the information about the data packets communicated at port 80.
Example 8: Display Network Data Packets for Specific IP Address
We can monitor the specific host with the tcpdump command. For instance, the below command checks the data packet details over the ens33 interface for the specific host IP address:
$ sudo tcpdump -i ens33 host 192.168.141.130
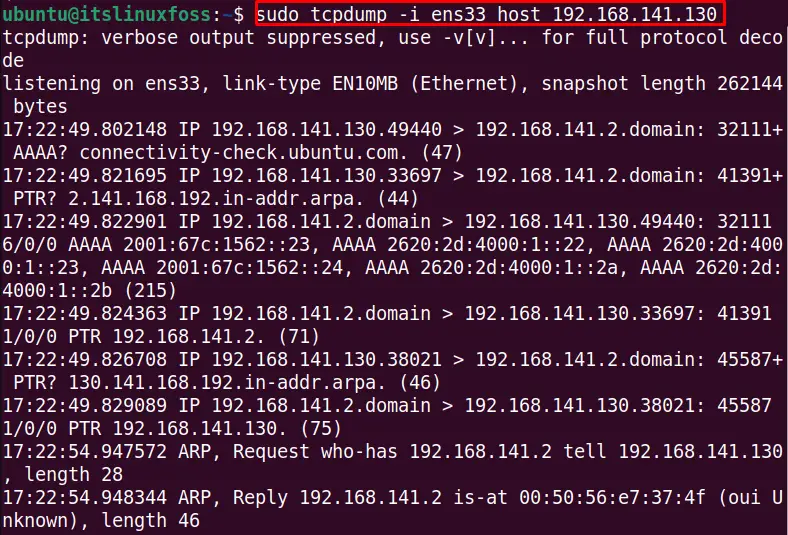
The host ens33 communication details are listed in the output.
Example 9: Use tcpdump for UDP Packets
The tcpdump, as the name indicates, captures the TCP packets and dumps them. But the tcpdump can also capture non-TCP traffic, such as ICMP or UDP. To capture the UDP packets for the ens33 interface, run this command in the terminal:
$ sudo tcpdump -i ens33 udp -v
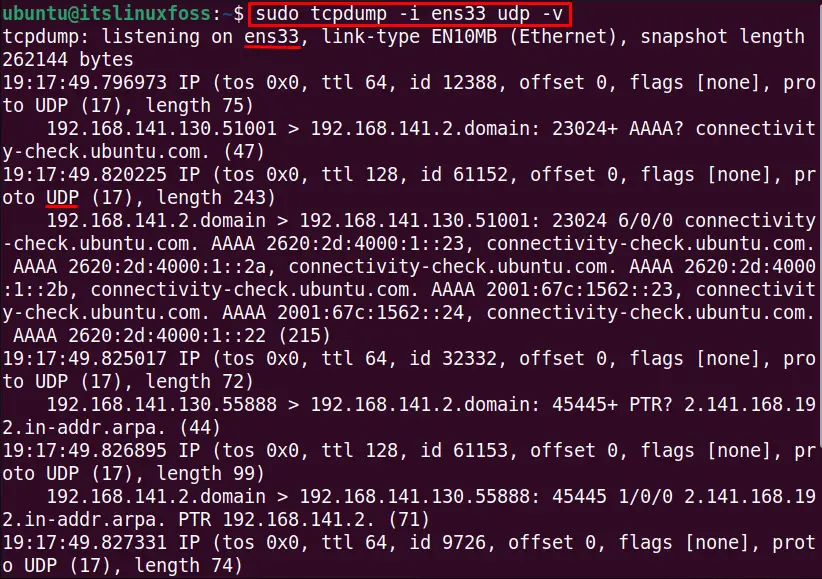
The output displays the UDP packet information for the ens33 interface.
Example 10: Use tcpdump for Address Resolution Protocol
Users can locate link-layer addresses, such as MAC addresses, using Address Resolution Protocol. Usually, the ARP is associated with an IPv4 address at the internet layer. To find the address resolution protocol for the interface ens33 and show its details with the “v” verbose option, execute this command:
$ sudo tcpdump -i ens33 arp -v
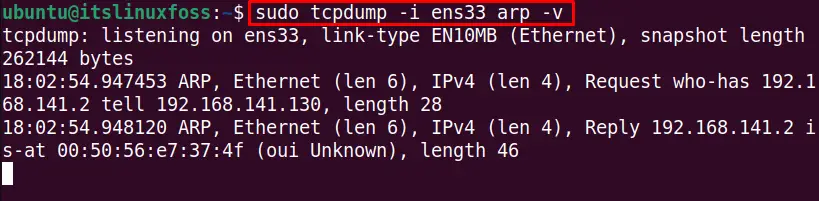
The output shows the data that contains the arp packets.
Conclusion
The tcpdump is a data packets analyzer tool over the internet that shows the details about these communication packets that are very useful for network security applications. The tcpdump command is explained thoroughly in this guide which can help beginners to learn a lot about this command.
Moreover, the tcpdump command can also be utilized for non-TCP packets, such as UDP, which is discussed with examples.
