One of the first things to validate when configuring a firewall or troubleshooting network connectivity problems is which ports are open or closed on your Ubuntu system.
This article discusses various methods for determining which ports on your Linux system are open to the outside world.
What is an Open port?
An application that works and listens on your network port is known as a listening port. Users can get a list of the system’s listening porBecause attackers can use open ports to exploit vulnerabilities or carry out other kinds of attacks, this can cause a security risk. Only the ports needed for your application’s functionality should be exposed, with all other ports closed.ts by using commands like netstat, ss, or lsof to query the network stack. Using a firewall, each listening port can be opened or closed. Any network port that receives and takes the incoming packets from various distant locations is known as an open port.
Because attackers can use open ports to exploit vulnerabilities or carry out other kinds of attacks, this can cause a security risk. Only the ports needed for your application’s functionality should be exposed, with all other ports closed.
Use nmap to check for open ports:
Nmap is a network scanning utility capable of scanning both large networks and single hosts. It is mostly used for penetration tests and security audits.
Talking about port scans, nmap should be your first choice to use. Nmap can detect the OS type, Mac address, kernel versions, and much more in addition to port scanning.
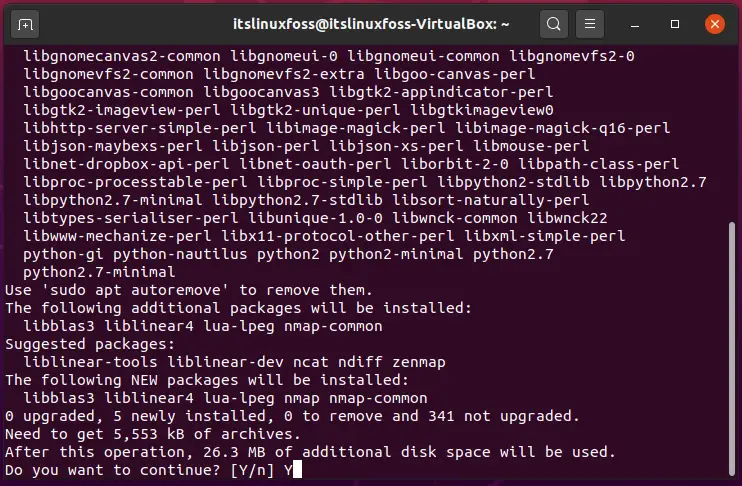
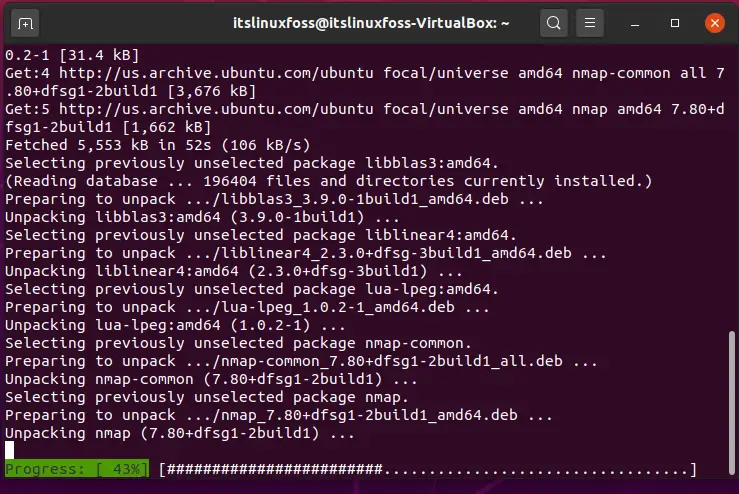
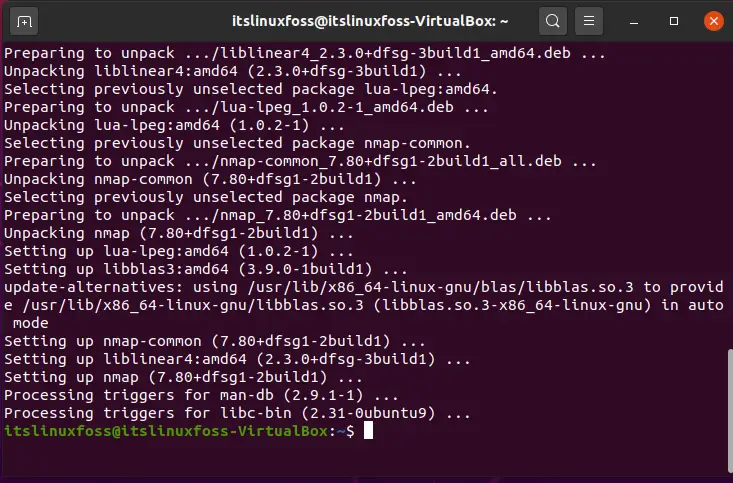
If you don’t have nmap on Ubuntu install it at first.
$ sudo apt install nmap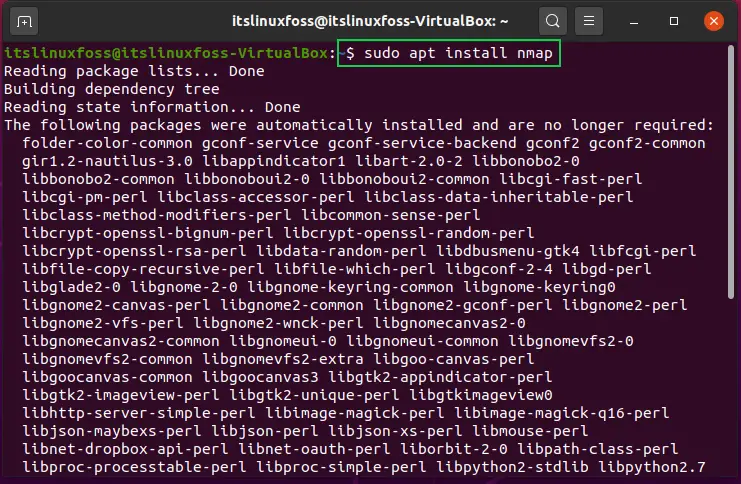
Listening ports from the network can be determined for TCP connections by issuing this command from the terminal:
$ sudo nmap -sT -p- 10.10.8.8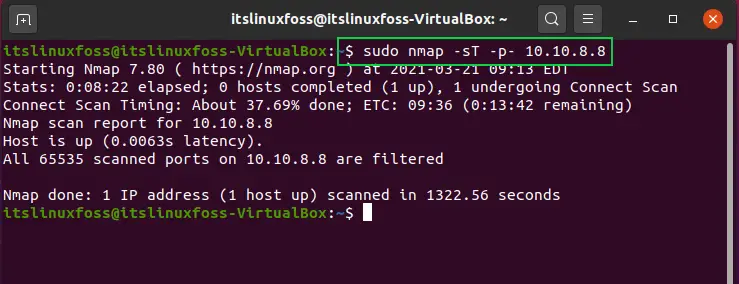
For scanning of UDP ports, utilize -sU in the command instead of -sT.
$ sudo nmap -sU -p- 10.10.8.8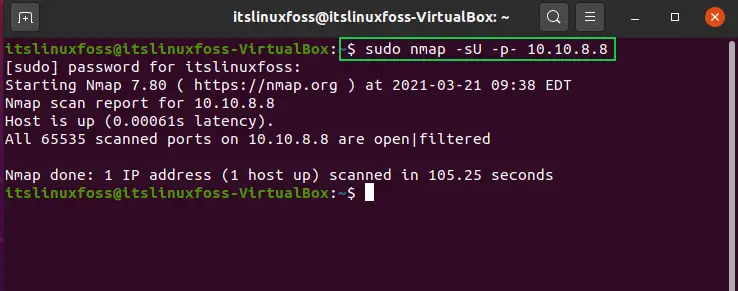
Using netcat to check open port:
Nc or netcat is a tool based on command-line which utilizes the UDP or TCP protocols for writing and reading data through several network connections. Netcat can scan a range of ports or a single port.
With IP address 10.10.8.8 in between 20-80 if you want for scanning the open TCP ports on a remote machine:
$ nc -z -v 10.10.8.8 20-80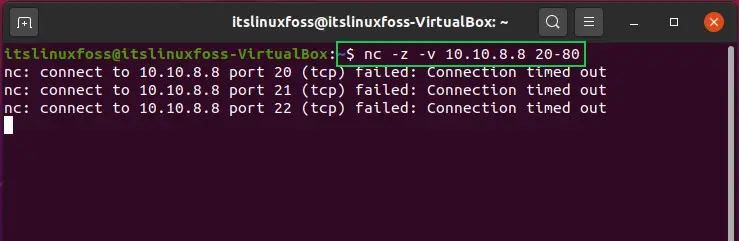
The -z option instructs nc to scan only for open ports and not send any data, while the -v option provides more detailed information.
Filter the results with the grep command if you only print out the open ports on the display with the lines.
$ nc -z -v 10.10.8.7 20-80 2>&1 | grep succeeded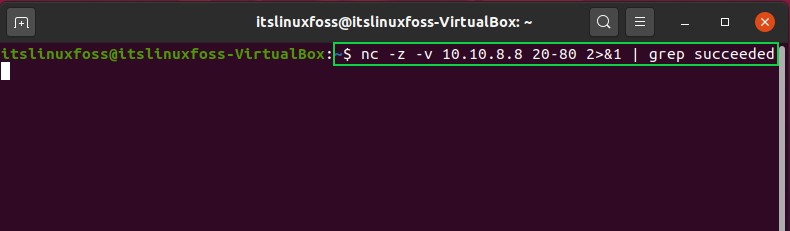
Utilize the -u option in the command to scan for UDP ports.
$ nc -z -v -u 10.10.8.7 20-80 2>&1 | grep succeeded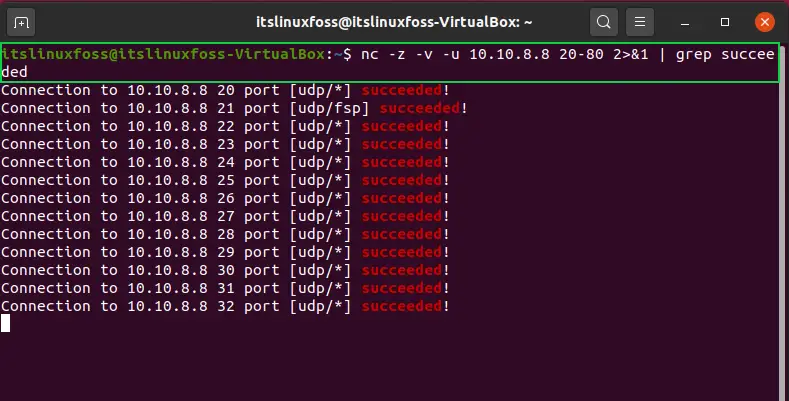
Conclusion:
We’ve shown you how to scan for open ports by using some tools like nmap and netcat. You can also checkout for open ports using other utilities and procedures such as the curl, Python socket module, telnet, or wget.

TUTORIALS ON LINUX, PROGRAMMING & TECHNOLOGY